export const config = { style: "enhanced" };
function pulseStateEventKey(input, env) {
const contextKey = env.event?.context?.trigger?.pulseStateMemory?.key;
return String(contextKey || input?.pulseStateEventKey || input?.eventKey || input?.eventId || "")
.trim()
.slice(0, 160);
}
export default async function handler(input, env) {
const channelId = String(env.pulse.DISCORD_CHANNEL_ID || "").trim();
if (!/^\d{17,22}$/.test(channelId) || !env.secrets.has("DISCORD_BOT_TOKEN")) {
return Response.json(
{ error: "Add DISCORD_CHANNEL_ID in .pulse and DISCORD_BOT_TOKEN in Pulse Secrets." },
{ status: 500 }
);
}
const message = String(input?.message || "").trim();
if (!message) {Blueprints
on Vibecodr.Space
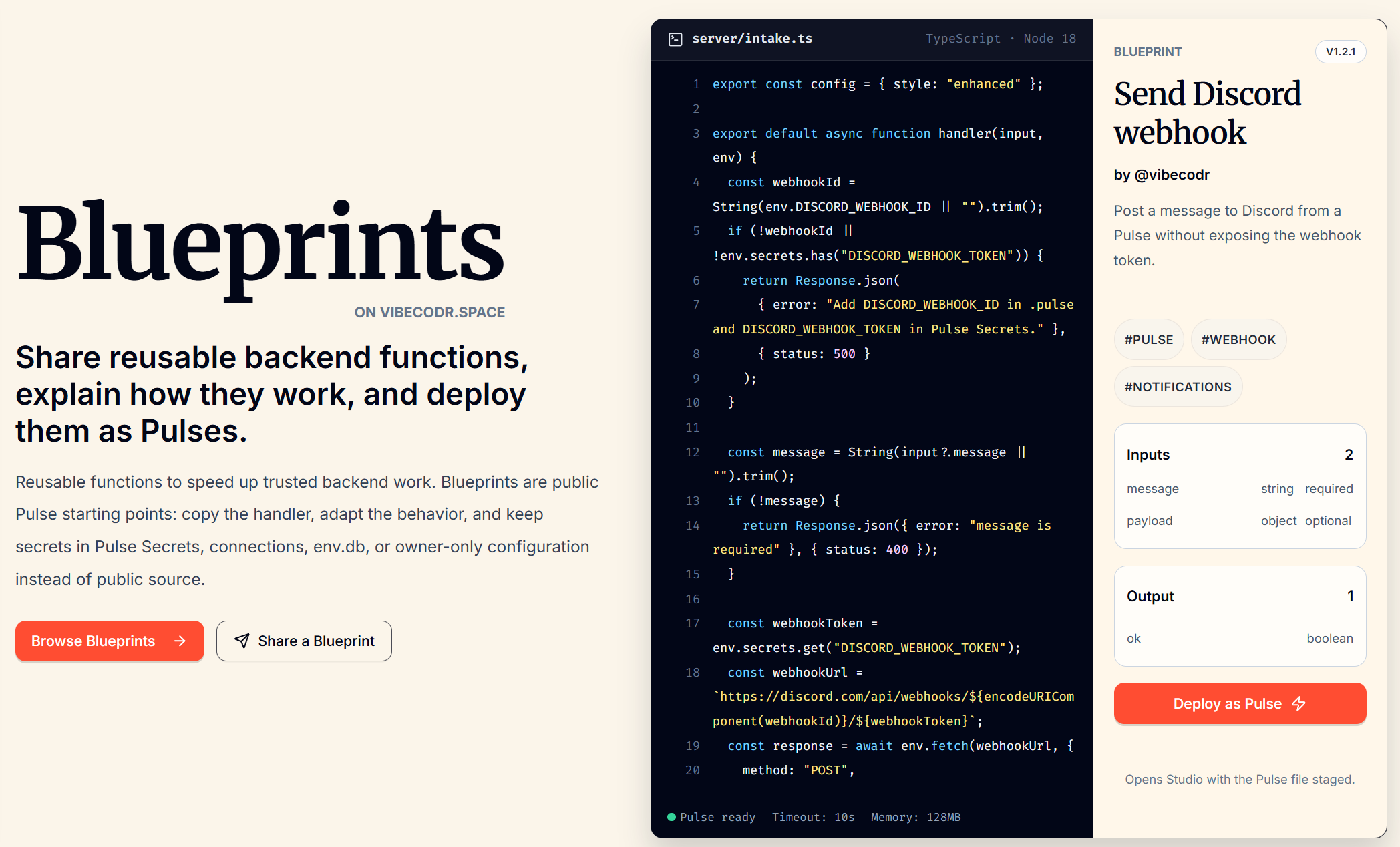
Share reusable backend functions, explain how they work, and deploy them as Pulses.
Reusable functions speed up trusted backend work. Blueprints are public Pulse starting points: copy the handler, adapt the behavior, put caller-safe config in env.pulse, and keep secrets or connections in private owner setup instead of public source.
Public blueprint code must not contain secrets, credentials, tokens, or external API keys. The crawler-facing directory mirrors the same public catalog humans browse in the app and links each item to its canonical detail page.
Public Pulse starting points
-
pulse · v1.0.0
Send Discord message
Post a message to a Discord channel from a Pulse without exposing the bot token.
secret: DISCORD_BOT_TOKEN, pulse: DISCORD_CHANNEL_ID, state: discordMessages, review: External call
-
pulse · v1.0.0
Fetch weather by city
Return current weather for any city name using Open-Meteo geocoding.
review: External call
-
pulse · v1.0.0
Create Notion database page
Create a Notion database page with a Notion API key kept in Pulse Secrets.
secret: NOTION_API_KEY, pulse: NOTION_DATABASE_ID, state: notionPageWrites, review: External call
-
pulse · v1.0.0
Pulse JSON intake
Receive JSON webhooks with event filtering and duplicate-protection metadata.
No required setup beyond reviewing the handler before deployment.
-
pulse · v1.0.0
Stripe webhook duplicate protection
Verify Stripe signatures before running webhook work once with Pulse State.
secret: STRIPE_WEBHOOK_SECRET, state: stripeWebhookEvents, review: Webhook duplicate policy
-
pulse · v1.0.0
HTTP mutation duplicate protection
Require Idempotency-Key for a POST mutation and protect the work with Pulse State.
state: httpMutations, review: Duplicate protection policy
-
pulse · v1.0.0
Route support message
Validate a support request, route it with public .pulse config, and log safe metadata.
No required setup beyond reviewing the handler before deployment.
-
pulse · v1.0.0
Pulse CORS reply
Return a narrow CORS response for a trusted Pulse endpoint.
pulse: ALLOWED_ORIGINS
-
pulse · v1.0.0
Request timer
Measure Pulse work or an HTTPS endpoint with structured timing logs.
No required setup beyond reviewing the handler before deployment.